OP Auto Clicker is open source, code-signed, and verified clean on VirusTotal across 70+ antivirus engines. No bundleware. No telemetry. No ads. No internet connection. Every release is reviewed publicly on GitHub before distribution.
Auto clickers have a sketchy reputation, and rightly so — the category is full of bundleware, ad-injectors, and outright malware shipped under "free" labels. OP Auto Clicker fixes that with a different model: full source on GitHub, every release signed and scanned, zero network calls, and a hard rule against bundling.
Below are the four pieces of evidence you can verify yourself, plus what to do if your antivirus throws a false positive (which happens to every auto clicker, ours included).
Six independently verifiable safety signals.
Scanned by every major AV engine on every release. Submit the SHA256 yourself to verify.
Every .exe is digitally signed with the project's release key. Tampering breaks the signature.
Full source code on GitHub. Audit it line-by-line. Build your own .exe from source if you prefer.
No "offer screens", no toolbars, no third-party installers. The .exe is the entire app.
Zero network calls. Zero analytics. The binary doesn't include any networking code at all.
It happens to every auto clicker. Here's why — and how to verify.
AV engines flag any program that sends synthetic mouse input — a pattern shared with malware.
Upload the .exe to virustotal.com. Across all 70+ engines, OP Auto Clicker shows clean.
If your AV still complains, add OP Auto Clicker to its exception list.
Yes. OP Auto Clicker is open source, code-signed, and verified clean by VirusTotal across 70+ antivirus engines. No bundleware, no ads, no telemetry. The full source code is on GitHub for independent inspection.
No. OP Auto Clicker passes VirusTotal scans with zero detections. The .exe is digitally signed, and the source is public on GitHub. Each release is scanned and signed before distribution.
Auto-clickers send synthetic input — a behavior shared with malware, so heuristic AV engines occasionally false-positive on any auto clicker. Submit the file to VirusTotal: it shows clean across major engines.
No. OP Auto Clicker collects zero data. It doesn't connect to the internet at all — no telemetry, no analytics, no auto-update calls. What runs on your PC stays on your PC.
Yes. The full source code is publicly available on GitHub under a permissive open-source license. Anyone can audit the code, build their own copy, or contribute fixes.
SmartScreen warns about any executable that hasn't built up a Microsoft "reputation" through millions of installs via the Microsoft Store. The warning is based on novelty, not threat. Click "More info" then "Run anyway" to launch.
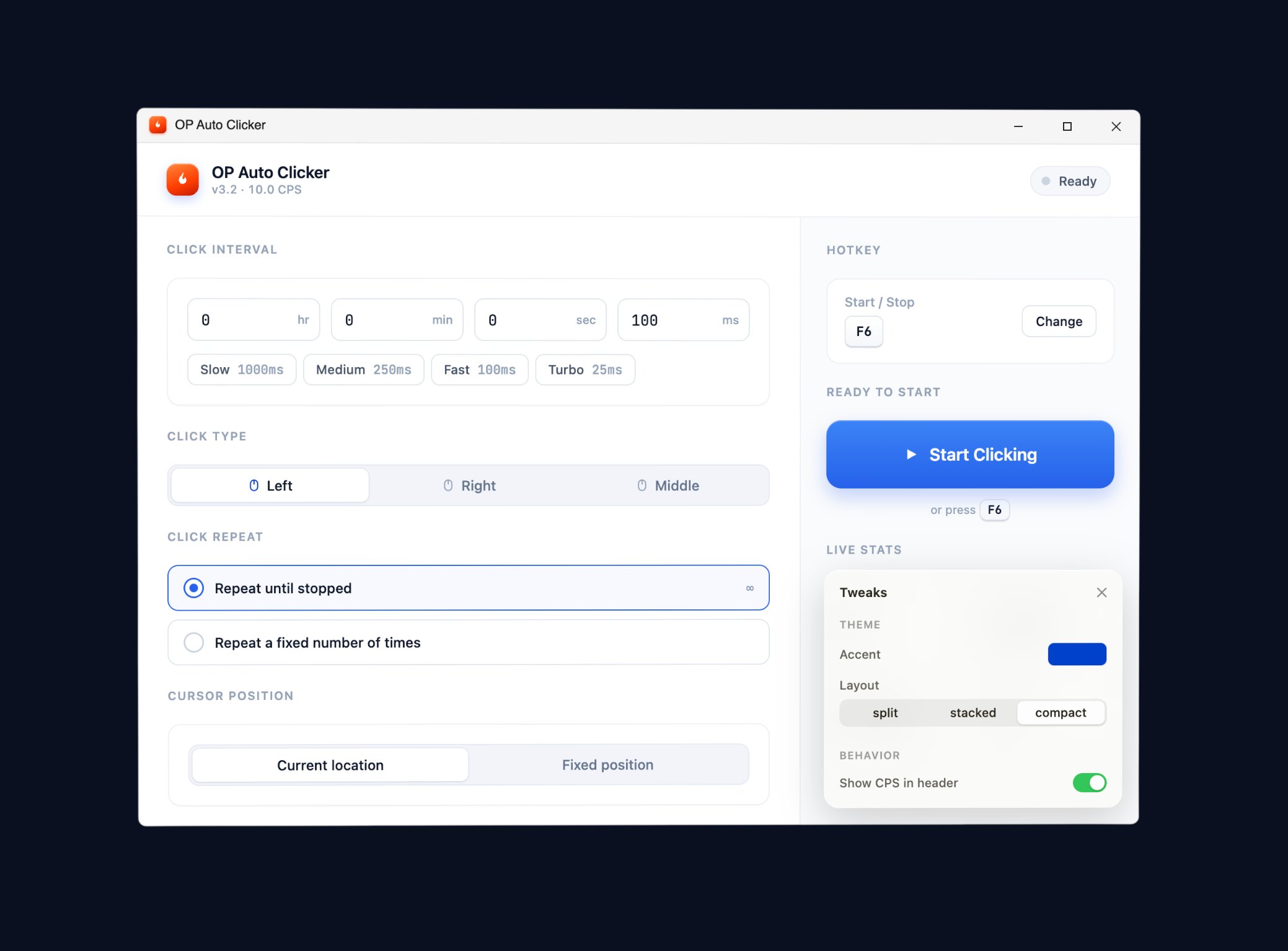
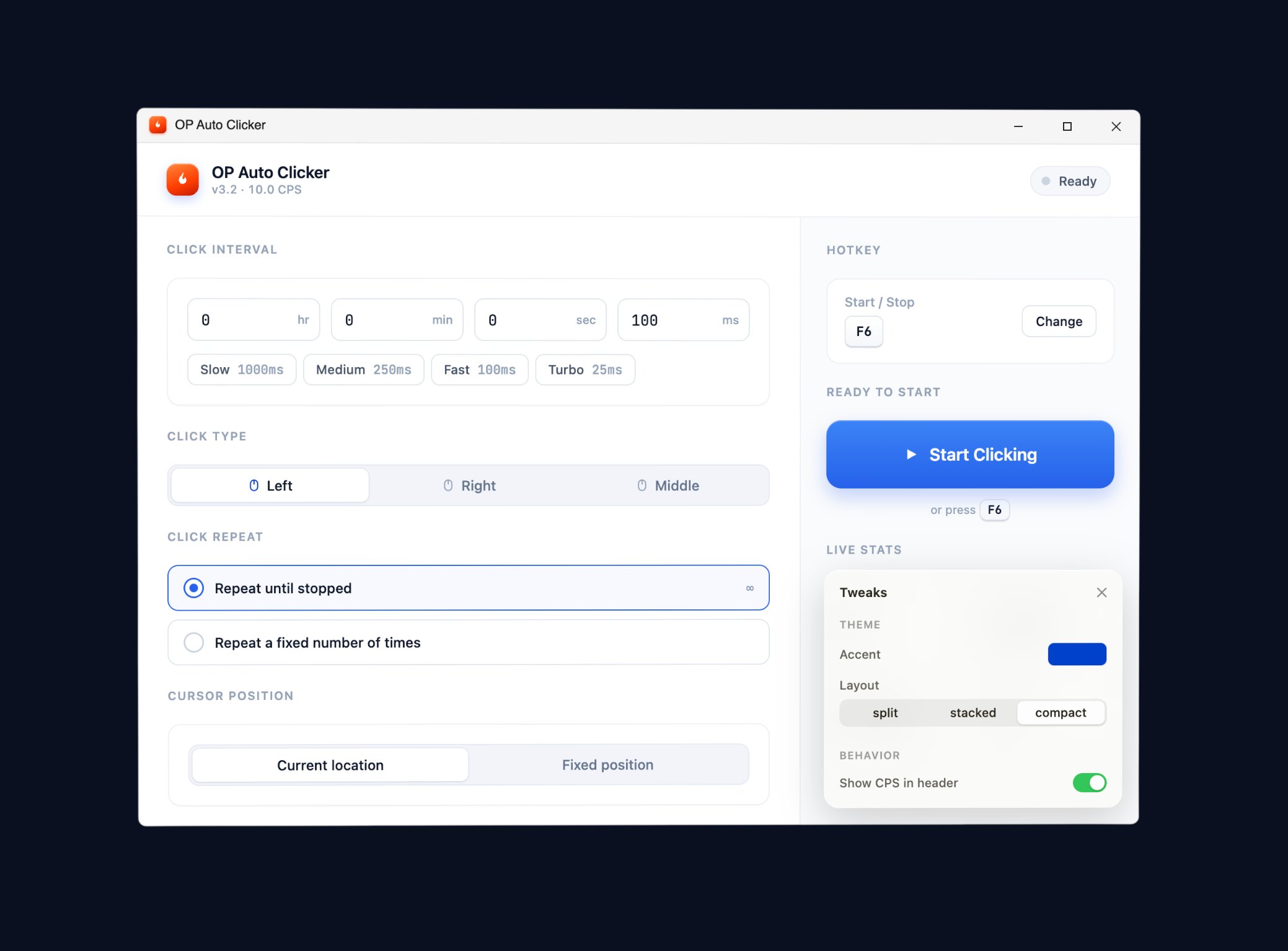
Six checks anyone can run before installing.
Right-click the .exe → Properties → Digital Signatures. OP Auto Clicker is signed by the project's release key.
Run certutil -hashfile OPAutoClicker.exe SHA256 and compare to the hash on the download page. Match = file is genuine.
Upload the .exe to virustotal.com. OP Auto Clicker shows clean across 70+ engines.
Open Resource Monitor or Wireshark. OP Auto Clicker makes zero outbound connections — ever.
Read every line of the OP Auto Clicker source. Build it yourself with Visual Studio if you want to be 100% sure.
OP Auto Clicker is exactly 512 KB. A "5 MB OP Auto Clicker" download from a third-party site is repackaged with bundleware — don't run it.
Bundleware risk is what separates the safe ones from the rest.
| OP Auto Clicker | Typical "free" auto clicker | |
|---|---|---|
| Open source | Yes | No |
| Code-signed binary | Yes | Sometimes |
| Bundleware in installer | None | Frequent |
| Telemetry / phone-home | None | Often present |
| Ad injection | None | Sometimes |
| SHA256 hash published | Yes | Rarely |
| VirusTotal scan public | Yes (every release) | Rarely |
| Requires admin install | No (portable) | Usually yes |